node-env-resolver Makes Safe, Typed Node Config the Default
23 Apr 2026Liran Tal is spot on in his Environment variables and configuration anti-patterns in Node.js applications post
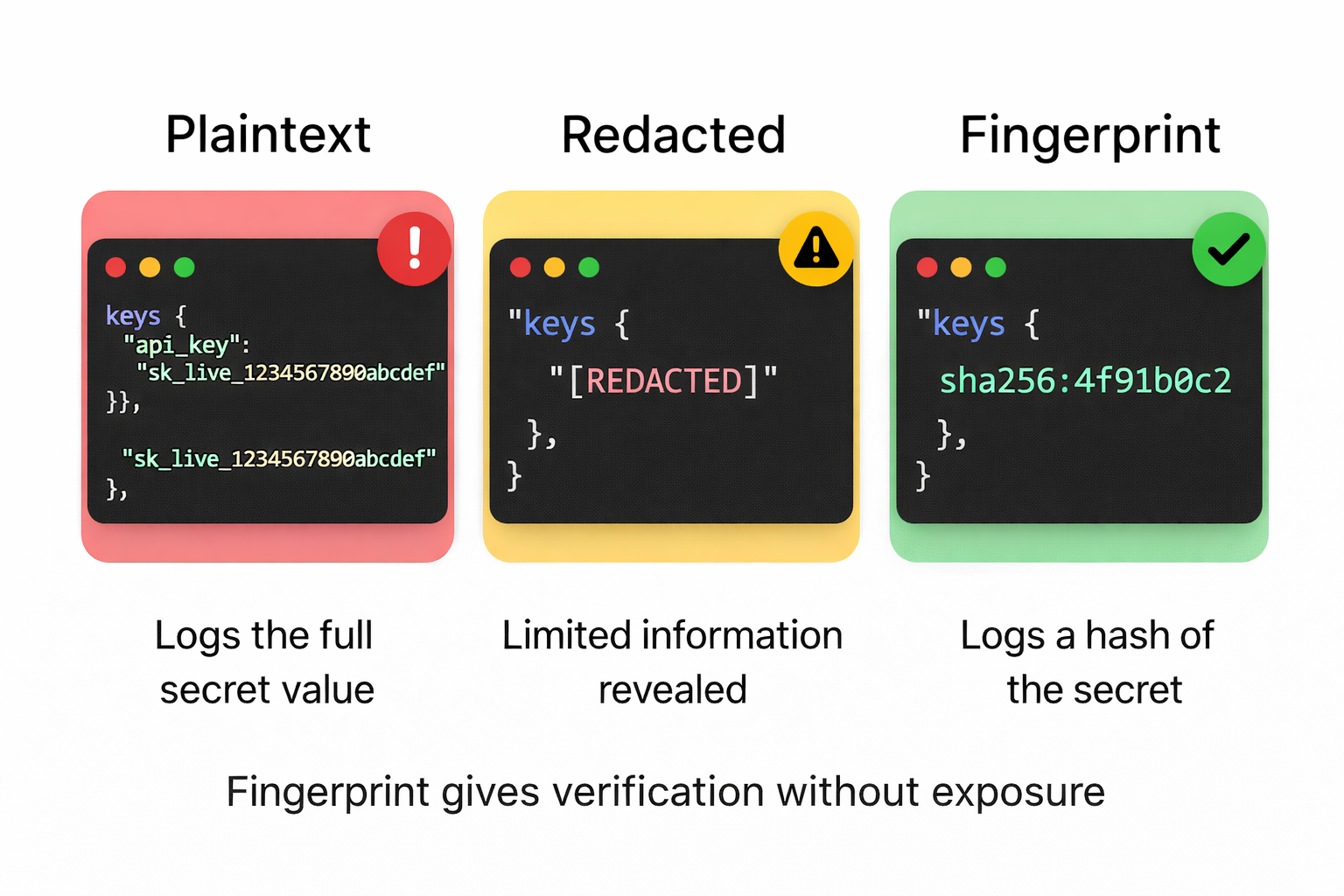
You may inadvertently expose sensitive information like database credentials and API keys as part of error messages, stack traces, and other forms of data returned to consuming clients.
He explains why process.env feels safe right up until it isn't.
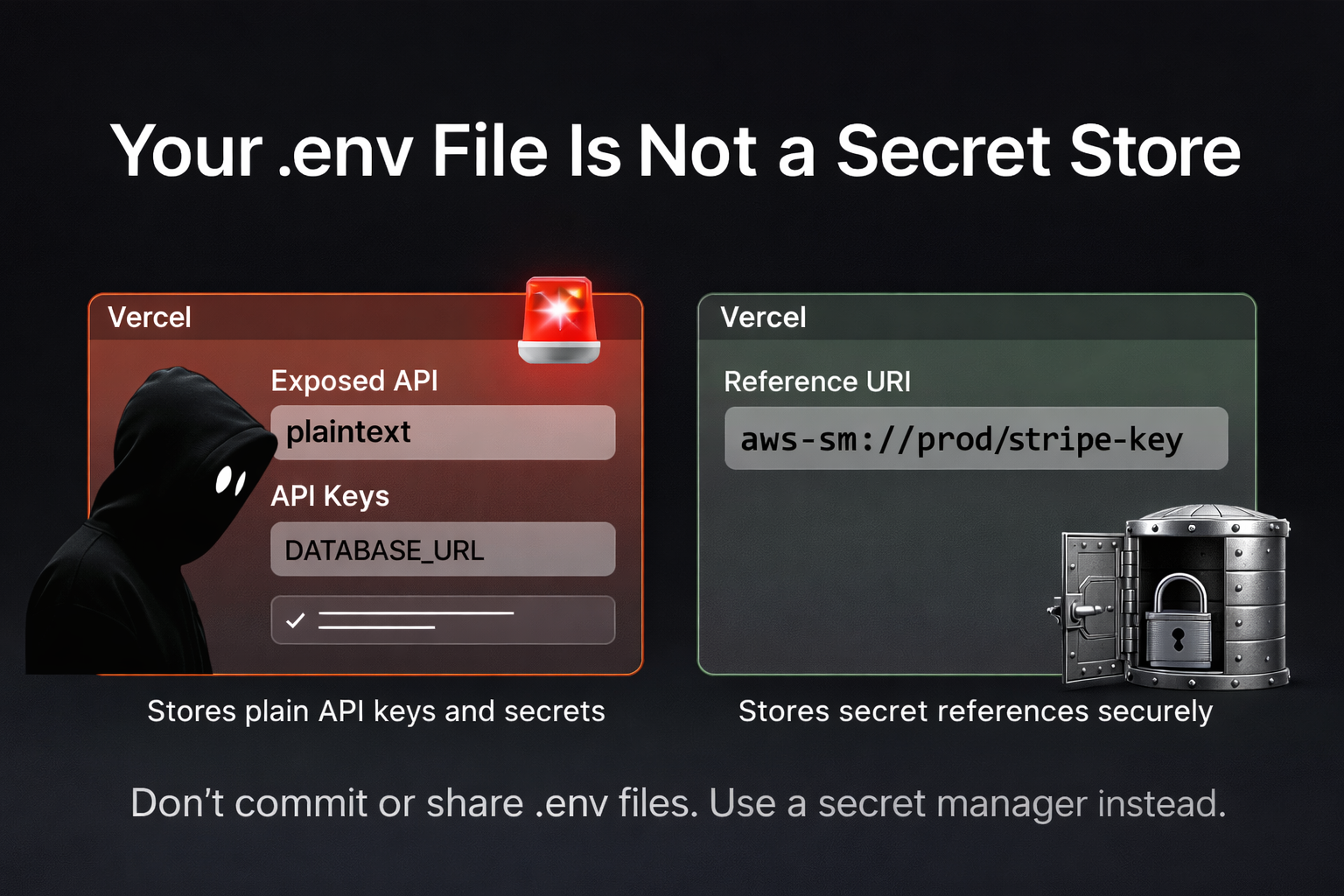
You add dotenv.config() on line one, scatter process.env.DB_PASSWORD across twelve files, then someone's error reporter serialises a request object and your Stripe key ends up in a third-party log.
If you've shipped a Node app, you've probably seen some version of this happen.
His anti-pattern example nails it:
const port = process.env.PORT || 3000;
const dbUsername = process.env.DB_USERNAME;
const dbPassword = process.env.DB_PASSWORD;
const dbHost = process.env.DB_HOST;
const apiBaseUrl = process.env.API_BASE_URL;
const apiToken = process.env.API_TOKEN;Untyped. Unvalidated. Globally readable. One step away from leaking through logs, traces, or error reporters.
But there's still a gap...
Read More →